Secure Information Management: Shielding Your Secret Information
Are you worried concerning the safety of your private details? In this article, we will review the value of protected data management and offer you with finest practices to secure your beneficial data. You'll discover common hazards to your information and how to implement effective data file encryption. We'll additionally explore the significance of gain access to controls and also customer authorizations, as well as the need for data backup as well as disaster recuperation procedures. Keep reading to make sure the safety of your sensitive information.
The Significance of Secure Information Monitoring
The significance of safe data monitoring can not be overemphasized in today's digital age. As an individual, you count on technology for various elements of your life, whether it's on-line financial, social networks, or keeping individual details. With the raising prevalence of cyber hazards, it is vital to focus on the security of your information.

When you handle your information firmly, you ensure that just authorized people have access to your private details. This protects you from identification burglary, monetary fraudulence, and also various other harmful activities. By applying strong passwords, encryption, as well as normal back-ups, you considerably decrease the threat of your information falling right into the incorrect hands
Furthermore, secure data administration additionally profits companies and organizations. As an organization proprietor, you have a duty to secure your customers' delicate information, such as credit scores card information or individual details. Failing to do so can result in reputational damages, lawful consequences, and also economic losses. By prioritizing secure information management techniques, you show your commitment to securing your consumers' personal privacy and also building count on within your area.
Typical Hazards to Confidential Details
Be aware of usual risks that can compromise your confidential information. Hackers can obstruct your data when you connect to unsafe networks, possibly exposing your financial and personal info. By being conscious of these typical dangers, you can take aggressive procedures to secure your personal information and ensure your online safety and security.
Best Practices for Information Encryption
When it comes to shielding your confidential details, data security is critical. File encryption converts your data right into a secret code, making it unreadable to unauthorized individuals.
To develop a solid and also special password, consider utilizing a combination of uppercase and also lowercase letters, numbers, as well as special characters. Avoid making use of typical expressions or easily guessable details, such as your name or birthdate. Additionally, refrain from making use of the same password for multiple accounts. In this manner, also if one password is jeopardized, your various other accounts stay safe.
Bear in mind to frequently upgrade your passwords to keep a high level of safety. Set pointers to transform your passwords every few months or whenever there is a data breach. By doing so, you minimize the danger of someone acquiring unapproved access to your secret information.
Implementing Gain Access To Controls as well as Customer Consents
Ensure that you consistently evaluate as well as adjust accessibility controls and also user approvals to preserve the safety and security of your sensitive information. By carrying out effective gain access to controls and customer permissions, you can substantially decrease the risk of unapproved accessibility to your personal details.
Begin by consistently evaluating the access manages in place. This includes reviewing who has accessibility to what data and also making sure that it aligns with their duties and also obligations within the organization. As staff members leave the business or join, it is essential to without delay update their access privileges to prevent any kind of possible violations.
In enhancement to reviewing access controls, it is necessary to adjust individual permissions as required. User permissions determine what activities an individual can perform on the information they have access to. By granting the appropriate level of approvals per individual, you can restrict their abilities and decrease the danger of information misuse or unintended deletion.
Frequently reviewing as well as adjusting gain access to controls and also customer consents is a recurring process - Managed IT Services. As your organization progresses and expands, it is vital to stay up to visit date with modifications as well as make sure that your information continues to be safe and secure. By doing so, you can safeguard your sensitive info from unauthorized gain access to and also preserve the stability and also discretion of your information
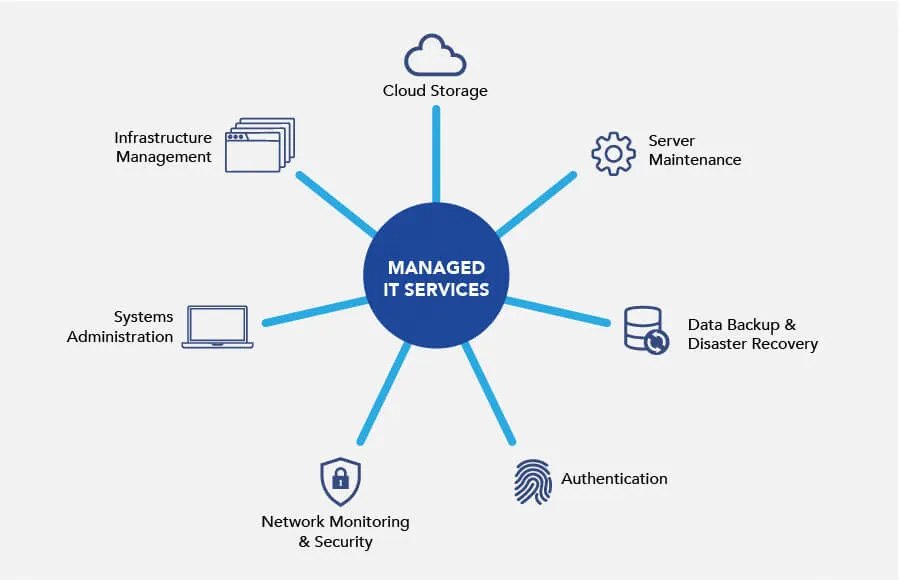
Data Backup as well as Calamity Healing Procedures
Frequently backing up your data is vital for calamity recuperation in instance of unforeseen occasions. It is important to have a back-up strategy in location to safeguard your useful information and make certain company continuity. By frequently backing up your information, you can minimize the effect of information loss because of equipment failings, natural catastrophes, or cyberattacks.
Having a trusted backup system allows you to recover your information rapidly and successfully, reducing downtime and preventing potential economic losses. Whether you pick to back up your data on external tough drives, cloud storage, or a mix of both, it is vital to set up regular back-ups to guarantee that your most current info is secured.
In addition to regular backups, it is just as important to evaluate your back-up systems and processes frequently. This makes sure that your backups are functioning effectively as well as that you can successfully recover your information when required. By examining your backup systems, you can identify any kind of prospective issues or voids in your disaster healing strategy as well as address them proactively.
Conclusion
Finally, managing and safeguarding your private details is critical in today's electronic landscape. Video Conferencing. By implementing safe data administration techniques such as security, accessibility controls, and also information backup measures, you can protect your useful information from typical threats. Keep in mind to routinely upgrade your safety and security procedures to stay one action in advance of potential breaches. By focusing on the protection of your secret information, you can guarantee the count on as well as self-confidence of your customers and also stakeholders. So, don't wait any longer, act now to secure your data!
In this write-up, we will discuss the significance of safe and secure information monitoring and give you with best practices to shield your important information. When you manage your data firmly, you make sure that only accredited individuals have access to your private info. When it comes to shielding your private details, data encryption is critical. By frequently backing up your information, you can straight from the source minimize the impact of information i was reading this loss due to equipment failings, all-natural catastrophes, or cyberattacks.
By carrying out secure data monitoring techniques such as security, access controls, and data backup procedures, you can guard your useful information from typical threats.